|
4 Context of the organization
|
|
|
| 4.1 Understanding the organization and its contextThe organization shall determine external and internal issues that are relevant to its purpose and that affect its ability to achieve the intended outcome(s) of its information security management system.NOTE: Determining these issues refers to establishing the external and internal context of the organization considered in Clause 5.3.1 of ISO 31000.4.2 Understanding the needs and expectations of interested parties
The organization shall determine:
a) interested parties that are relevant to the information security management system; and
b) the requirements of these interested parties relevant to information security.
NOTE: The requirements of interested parties may include legal and regulatory requirements and contractual obligations. |
|
4.2 Establishing and managing the ISMS4.2.1 Establish the ISMSThe organization shall do the following.b) Define an ISMS policy in terms of the characteristics of the business, the organization, its location, assets and technology that:
2) takes into account business and legal or regulatory requirements, and contractual security obligations; |
|
4 Context of the organization
|
|
|
| 4.3 Determining the scope of the information security management system The organization shall determine the boundaries and applicability of the information security management system to establish its scope.When determining this scope, the organization shall consider:a) the external and internal issues referred to in 4.1;
b) the requirements referred to in 4.2; and
c) interfaces and dependencies between activities performed by the organization, and those that are performed by other organizations.
The scope shall be available as documented information.
4.4 Information security management system
The organization shall establish, implement, maintain and continually improve an information security management system, in accordance with the requirements of this International Standard. |
|
4.2 Establishing and managing the ISMS4.2.1 Establish the ISMSThe organization shall do the following.a) Define the scope and boundaries of the ISMS in terms of the characteristics of the business, the organization, its location, assets and technology, and including details of and justification for any exclusions from the scope (see 1.2).
|
|
5 Leadership
|
|
|
| 5.1 Leadership and commitmentTop management shall demonstrate leadership and commitment with respect to the information security management system by:a) ensuring the information security policy and the information security objectives are established and are compatible with the strategic direction of the organization;b) ensuring the integration of the information security management system requirements into the organization’s processes;
c) ensuring that the resources needed for the information security management system are available;
d) communicating the importance of effective information security management and conforming to the information security management system requirements;
e) ensuring that the information security management system achieves its intended outcome(s);
f) directing and supporting persons to contribute to the effectiveness of the information security management system;
g) promoting continual improvement; and
h) supporting other relevant management roles to demonstrate their leadership as it applies to their areas of responsibility. |
|
5.1 Management commitmentManagement shall provide evidence of its commitment to the establishment, implementation, operation, monitoring, review, maintenance and improvement of the ISMS by:a) establishing an ISMS policy;b) ensuring that ISMS objectives and plans are established;
c) establishing roles and responsibilities for information security;
d) communicating to the organization the importance of meeting information security objectives and conforming to the information security policy, its responsibilities under the law and the need for continual improvement;
e) providing sufficient resources to establish, implement, operate, monitor, review, maintain and improve the ISMS (see 5.2.1);
f) deciding the criteria for accepting risks and the acceptable levels of risk;
g) ensuring that internal ISMS audits are conducted (see 6); and
h) conducting management reviews of the ISMS (see 7). |
|
5 Leadership
|
|
|
| 5.2 Policy Top management shall establish an information security policy that:a) is appropriate to the purpose of the organization;b) includes information security objectives (see 6.2) or provides the framework for setting information security objectives;
c) includes a commitment to satisfy applicable requirements related to information security; and
d) includes a commitment to continual improvement of the information security management system.
The information security policy shall:
e) be available as documented information;
f) be communicated within the organization; and
g) be available to interested parties, as appropriate. |
|
4.2 Establishing and managing the ISMS4.2.1 Establish the ISMSThe organization shall do the following.b) Define an ISMS policy in terms of the characteristics of the business, the organization, its location, assets and technology that:
1) includes a framework for setting objectives and establishes an overall sense of direction and principles for action with regard to information security;
2) takes into account business and legal or regulatory requirements, and contractual security obligations;
3) aligns with the organization’s strategic risk management context in which the establishment and maintenance of the ISMS will take place;
4) establishes criteria against which risk will be evaluated (see 4.2.1c)); and
5) has been approved by management. |
|
5 Leadership
|
|
|
| 5.3 Organizational roles, responsibilities and authoritiesTop management shall ensure that the responsibilities and authorities for roles relevant to information security are assigned and communicated.Top management shall assign the responsibility and authority for:a) ensuring that the information security management system conforms to the requirements of this International Standard; and
b) reporting on the performance of the information security management system to top management.
NOTE: Top management may also assign responsibilities and authorities for reporting performance of the information security management system within the organization.
|
|
5.1 Management commitmentManagement shall provide evidence of its commitment to the establishment, implementation, operation, monitoring, review, maintenance and improvement of the ISMS by:c) establishing roles and responsibilities for information security;e) providing sufficient resources to establish, implement, operate, monitor, review, maintain and improve the
ISMS (see 5.2.1);
|
|
6 Planning
|
|
|
| 6.1 Actions to address risks and opportunities6.1.1 General When planning for the information security management system, the organization shall consider the issues referred to in 4.1 and the requirements referred to in 4.2 and determine the risks and opportunities that need to be addressed to:a) ensure the information security management system can achieve its intended outcome(s);
b) prevent, or reduce, undesired effects; and
c) achieve continual improvement.
The organization shall plan:
d) actions to address these risks and opportunities, and
e) how to
1) integrate and implement these actions into its information security management system processes; and
2) evaluate the effectiveness of these actions. |
|
|
|
6 Planning
|
|
|
| 6.1.2 Information security risk assessment The organization shall define and apply an information security risk assessment process that:a) establishes and maintains information security risk criteria that include:1) the risk acceptance criteria; and
2) criteria for performing information security risk assessments;
b) ensures that repeated information security risk assessments produce consistent, valid and comparable results;
c) identifies the information security risks:
1) apply the information security risk assessment process to identify risks associated with the loss of confidentiality, integrity and availability for information within the scope of the information
security management system; and
2) identify the risk owners
|
|
4.2 Establishing and managing the ISMS4.2.1 Establish the ISMSThe organization shall do the following.c) Define the risk assessment approach of the organization.
1) Identify a risk assessment methodology that is suited to the ISMS, and the identified business
information security, legal and regulatory requirements.
2) Develop criteria for accepting risks and identify the acceptable levels of risk. (see 5.1f)).
The risk assessment methodology selected shall ensure that risk assessments produce comparable and reproducible results.
NOTE: There are different methodologies for risk assessment. Examples of risk assessment methodologies are discussed in ISO/IEC TR 13335-3, Information technology — Guidelines for the management of IT Security —
Techniques for the management of IT Security.
d) Identify the risks.
1) Identify the assets within the scope of the ISMS, and the owners of these assets.
2) Identify the threats to those assets.
3) Identify the vulnerabilities that might be exploited by the threats.
4) Identify the impacts that losses of confidentiality, integrity and availability may have on the assets. |
|
6 Planning
|
|
|
| 6.1.2 Information security risk assessment d) analyses the information security risks:1) assess the potential consequences that would result if the risks identified in 6.1.2 c) 1) were to materialize;2) assess the realistic likelihood of the occurrence of the risks identified in 6.1.2 c) 1); and
3) determine the levels of risk;
e) evaluates the information security risks:
1) compare the results of risk analysis with the risk criteriaestablished in 6.1 .2 a);and
2) prioritize the analysed risks for risk treatment.
The organization shall retain documented information about the information security risk assessment process |
|
4.2 Establishing and managing the ISMS4.2.1 Establish the ISMSe) Analyse and evaluate the risks.1) Assess the business impacts upon the organization that might result from security failures, taking into
account the consequences of a loss of confidentiality, integrity or availability of the assets.
2) Assess the realistic likelihood of security failures occurring in the light of prevailing threats and vulnerabilities, and impacts associated with these assets, and the controls currently implemented.
3) Estimate the levels of risks.
4) Determine whether the risks are acceptable or require treatment using the criteria for accepting risks established in 4.2.1c)2). |
|
6 Planning
|
|
|
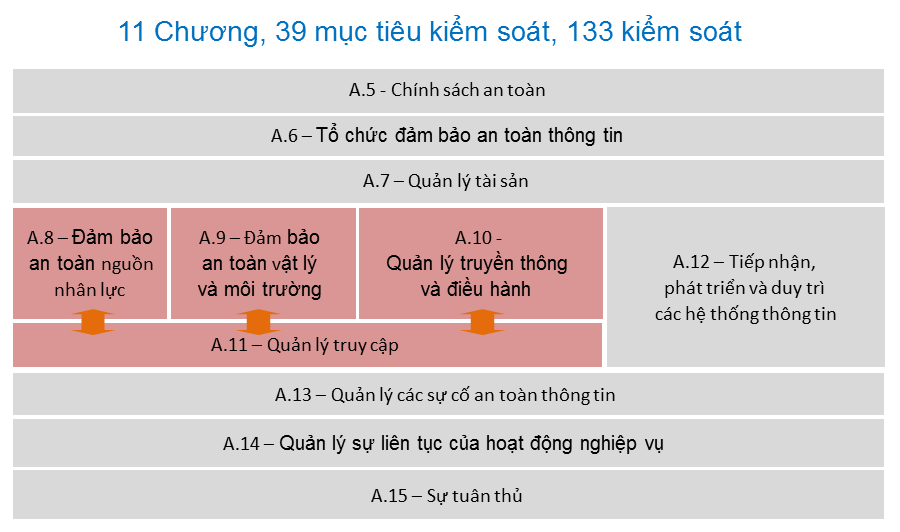
| 6.1.3 Information security risk treatmentThe organization shall apply an information security risk treatment process to:a) select appropriate information security risk treatment options, taking account of the risk assessment results;b) determine all controls that are necessary to implement the information security risk treatment option(s) chosen;
NOTE: Organizations can design controls as required, or identify them from any source.
c) compare the controls determined in 6.1.3 b) above with those in Annex A and verify that no necessary controls have been omitted;
NOTE 1: Annex A contains a comprehensive list of control objectives and controls. Users of this International Standard are directed to Annex A to ensure that no important control options are overlooked
NOTE 2: Control objectives are implicitly included in the controls chosen. The control objectives and controls listed in Annex A are not exhaustive and additional control objectives and controls may also be needed
|
|
4.2 Establishing and managing the ISMS4.2.1 Establish the ISMSThe organization shall do the following.f) Identify and evaluate options for the treatment of risks.
Possible actions include:
1) applying appropriate controls;
2) knowingly and objectively accepting risks, providing they clearly satisfy the organization’s policies and the criteria for accepting risks (see 4.2.1c)2));
3) avoiding risks; and
4) transferring the associated business risks to other parties, e.g. insurers, suppliers.
g) Select control objectives and controls for the treatment of risks.
Control objectives and controls shall be selected and implemented to meet the requirements identified by the risk assessment and risk treatment process. This selection shall take account of the criteria for accepting risks (see 4.2.1c)2)) as well as legal, regulatory and contractual requirements.
The control objectives and controls from Annex A shall be selected as part of this process as suitable to cover the identified requirements.
The control objectives and controls listed in Annex A are not exhaustive and additional control objectives and controls may also be selected.
NOTE: Annex A contains a comprehensive list of control objectives and controls that have been found to be commonly relevant in organizations. Users of this International Standard are directed to Annex A as a starting point for control selection to ensure that no important control options are overlooked.
h) Obtain management approval of the proposed residual risks.
i) Obtain management authorization to implement and operate the ISMS. |
|
6 Planning
|
|
|
| 6.1.3 Information security risk treatmentd) produce a Statement of Applicability thatcontains the necessary controls (see 6.1.3 a), b) and c)) and justification for inclusions,-whether they are implemented or not, and
-the justification for exclusions of controls in Annex A;
e) formulate an information security risk treatment plan;
f) obtain risk owner’s approval of the information security risk treatment plan and the acceptance of the residual information security risks.
The organization shall retain documented information about the information security risk treatment process.
NOTE: The information security risk assessment and treatment process in this International Standard aligns with the principles and generic guidelines provided in ISO 31000. |
|
4.2 Establishing and managing the ISMS4.2.1 Establish the ISMSh) Obtain management approval of the proposed residual risks.i) Obtain management authorization to implement and operate the ISMS.
j) Prepare a Statement of Applicability.
A Statement of Applicability shall be prepared that includes the following:
1) the control objectives and controls selected in 4.2.1g) and the reasons for their selection;
2) the control objectives and controls currently implemented (see 4.2.1e)2)); and
3) the exclusion of any control objectives and controls in Annex A and the justification for their exclusion.
NOTE: The Statement of Applicability provides a summary of decisions concerning risk treatment. Justifying exclusions provides a cross-check that no controls have been inadvertently omitted.
4.2.2 Implement and operate the ISMS
The organization shall do the following.
a)Formulate a risk treatment plan that identifies the appropriate management action, resources, responsibilities and priorities for managing information security risks (see 5) |
|
6 Planning
|
|
|
| 6.2 Information security objectives and plans to achieve them The organization shall establish information security objectives at relevant functions and levels.The information security objectives shall:a) be consistent with the information security policy;
b) be measurable (if practicable);
c) take into account applicable information security requirements, and risk assessment and treatment results;
d) be communicated, and
e) be updated as appropriate.
The organization shall retain documented information on the information security objectives.
When planning how to achieve its information security objectives, the organization shall determine:
f) what will be done;
g) what resources will be required;
h) who will be responsible;
i) when it will be completed; and
j) how the results will be evaluated. |
|
5.1 Management commitmentManagement shall provide evidence of its commitment to the establishment, implementation, operation, monitoring, review, maintenance and improvement of the ISMS by:b) ensuring that ISMS objectives and plans are established;d) communicating to the organization the importance of meeting information security objectives and conforming to the information security policy, its responsibilities under the law and the need for continual improvement;
|
|
7 Support
|
|
|
| 7.1 ResourcesThe organization shall determine and provide the resources needed for the establishment, implementation, maintenance and continual improvement of the information security management system.7.2 CompetenceThe organization shall
a) determine the necessary competence of person(s) doing work under its control that affects its information security performance;
b) ensure that these persons are competent on the basis of appropriate education, training, or experience;
c) where applicable, take actions to acquire the necessary competence, and evaluate the effectiveness of the actions taken; and
d) retain appropriate documented information as evidence of competence.
NOTE: Applicable actions may include, for example: the provision of training to, the mentoring of, or the re-assignment of current employees; or the hiring or contracting of competent persons. |
|
5.2 Resource management5.2.1 Provision of resourcesThe organization shall determine and provide the resources needed to:a) establish, implement, operate, monitor, review, maintain and improve an ISMS;
b) ensure that information security procedures support the business requirements;
c) identify and address legal and regulatory requirements and contractual security obligations;
d) maintain adequate security by correct application of all implemented controls;
e) carry out reviews when necessary, and to react appropriately to the results of these reviews; and
f) where required, improve the effectiveness of the ISMS.
5.2.2 Training, awareness and competence
The organization shall ensure that all personnel who are assigned responsibilities defined in the ISMS are competent to perform the required tasks by:
a) determining the necessary competencies for personnel performing work effecting the ISMS;
b) providing training or taking other actions (e.g. employing competent personnel) to satisfy these needs;
c) evaluating the effectiveness of the actions taken; and
d) maintaining records of education, training, skills, experience and qualifications (see 4.3.3). |
|
7 Support
|
|
|
| 7.3 AwarenessPersons doing work under the organization’s control shall be aware of:a) the information security policy;b) their contribution to the effectiveness of the information security management system, including the benefits of improved information security performance; and
c) the implications of not conforming with the information security management system requirements.
7.4 Communication
The organization shall determine the need for internal and external communications relevant to the information security management system including:
a) on what to communicate;
b) when to communicate;
c) with whom to communicate;
d) who shall communicate; and
e) the processes by which communication shall be effected. |
|
5.2.2 Training, awareness and competenceThe organization shall also ensure that all relevant personnel are aware of the relevance and importance of their information security activities and how they contribute to the achievement of the ISMS objectives.
4.2.4 Maintain and improve the ISMS
The organization shall regularly do the following.
c) Communicate the actions and improvements to all interested parties with a level of detail appropriate to the circumstances and, as relevant, agree on how to proceed.
|
|
7 Support
|
|
|
| 7.5 Documented information7.5.1 GeneralThe organization’s information security management system shall include:a) documented information required by this International Standard; and
b) documented information determined by the organization as being necessary for the effectiveness of the information security management system.
NOTE: The extent of documented information for an information security management system can differ from one organization to another due to:
1) the size of organization and its type of activities, processes, products and services;
2) the complexity of processes and their interactions; and
3) the competence of persons. |
|
4.3 Documentation requirements4.3.1 GeneralDocumentation shall include records of management decisions, ensure that actions are traceable to management decisions and policies, and ensure that the recorded results are reproducible.It is important to be able to demonstrate the relationship from the selected controls back to the results of the risk assessment and risk treatment process, and subsequently back to the ISMS policy and objectives.
The ISMS documentation shall include:
a) documented statements of the ISMS policy (see 4.2.1b)) and objectives;
b) the scope of the ISMS (see 4.2.1a));
c) procedures and controls in support of the ISMS;
d) a description of the risk assessment methodology (see 4.2.1c));
e) the risk assessment report (see 4.2.1c) to 4.2.1g));
f) the risk treatment plan (see 4.2.2b));
g) documented procedures needed by the organization to ensure the effective planning, operation and control of its information security processes and describe how to measure the effectiveness of controls (see 4.2.3c));
h) records required by this International Standard (see 4.3.3); and
i) the Statement of Applicability.
NOTE 1: Where the term “documented procedure” appears within this International Standard, this means that the procedure is established, documented, implemented and maintained.
NOTE 2: The extent of the ISMS documentation can differ from one organization to another owing to:
- the size of the organization and the type of its activities; and
- the scope and complexity of the security requirements and the system being managed.
NOTE 3: Documents and records may be in any form or type of medium. |
|
7 Support
|
|
|
| 7.5.2 Create and updateWhen creating and updating documented information the organization shall ensure appropriate:a) identification and description (e.g. a title, date, author, or reference number);b) format (e.g. language, software version, graphics) and media (e.g. paper, electronic); and
c) review and approval for suitability and adequacy.
7.5.3 Control of documented Information
Documented information required by the information security management system and by this International Standard shall be controlled to ensure:
a) it is available and suitable for use, where and when it is needed; and
b) it is adequately protected (e.g. from loss of confidentiality, improper use, or loss of integrity).
For the control of documented information, the organization shall address the following activities, as applicable:
c) distribution, access, retrieval and use;
d) storage and preservation, including the preservation of legibility;
e) control of changes (e.g. version control); and
f) retention and disposition.
Documented information of external origin, determined by the organization to be necessary for the planning and operation of the information security management system, shall be identified as appropriate, and controlled.
NOTE: Access implies a decision regarding the permission to view the documented information only, or the permission and authority to view and change the documented information, etc.
|
|
4.3.2 Control of documentsDocuments required by the ISMS shall be protected and controlled. A documented procedure shall be established to define the management actions needed to:a) approve documents for adequacy prior to issue;b) review and update documents as necessary and re-approve documents;
c) ensure that changes and the current revision status of documents are identified;
d) ensure that relevant versions of applicable documents are available at points of use;
e) ensure that documents remain legible and readily identifiable;
f) ensure that documents are available to those who need them, and are transferred, stored and ultimately disposed of in accordance with the procedures applicable to their classification;
g) ensure that documents of external origin are identified;
h) ensure that the distribution of documents is controlled;
i) prevent the unintended use of obsolete documents; and
j) apply suitable identification to them if they are retained for any purpose.
4.3.3 Control of records
Records shall be established and maintained to provide evidence of conformity to requirements and the effective operation of the ISMS. They shall be protected and controlled. The ISMS shall take account of any relevant legal or regulatory requirements and contractual obligations. Records shall remain legible, readily identifiable and retrievable. The controls needed for the identification, storage, protection, retrieval, retention time and disposition of records shall be documente d and implemented.
Records shall be kept of the performance of the process as outlined in 4.2 and of all occurrences of significant security incidents related to the ISMS.
EXAMPLE
Examples of records are a visitors’ book, audit reports and completed access authorization forms. |
|
8 Operation
|
|
|
| 8.1 Operational planning and controlThe organization shall plan, implement and control the processes needed to meet information security requirements, and to implement the actions determined in 6.1.The organization shall also implement plans to achieve information security objectives determined in 6.2.The organization shall keep documented information to the extent necessary to have confidence that the processes have been carried out as planned.
The organization shall control planned changes and review the consequences of unintended changes, taking action to mitigate any adverse effects, as necessary.
The organization shall ensure that outsourced processes are determined and controlled.
8.2 Information security risk assessment
The organization shall perform information security risk assessments at planned intervals or when significant changes are proposed or occur, taking account of the criteria established in 6.1.2).
The organization shall retain documented information of the results of the information security risk assessments.
8.3 Information security risk treatment
The organization shall implement the information security risk treatment plan.
The organization shall retain documented information of the results of the information security risk treatment. |
|
4.2.3 Monitor and review the ISMSThe organization shall do the following.d) Review risk assessments at planned intervals and review the residual risks and the identified acceptable levels of risks, taking into account changes to:1) the organization;
2) technology;
3) business objectives and processes;
4) identified threats;
5) effectiveness of the implemented controls; and
6) external events, such as changes to the legal or regulatory environment, changed contractual obligations, and changes in social climate.
4.2 Establishing and managing the ISMS
4.2.2 Implement and operate the ISMS
The organization shall do the following.
b) Implement the risk treatment plan in order to achieve the identified control objectives, which includes consideration of funding and allocation of roles and responsibilities.
c) Implement controls selected in 4.2.1g) to meet the control objectives.
e) Implement training and awareness programes (see 5.2.2).
f) Manage operation of the ISMS.
g) Manage resources for the ISMS (see 5.2). |
|
9 Performance evaluation
|
|
|
| 9.1 Monitoring, measurement, analysis and evaluationThe organization shall evaluate the information security performance and the effectiveness of the information security management system.The organization shall determine:a) what needs to be monitored and measured, including information security processes and controls;
b) the methods for monitoring, measurement, analysis and evaluation, as applicable, to ensure valid results;
NOTE: The methods selected should produce comparable and reproducible results to be considered valid.
c) when the monitoring and measuring shall be performed;
d) who shall monitor and measure;
e) when the results from monitoring and measurement shall be analyzed and evaluated; and
f) who shall analyse and evaluate these results.
The organization shall retain appropriate documented information as evidence of the monitoring and measurement results. |
|
4.2 Establishing and managing the ISMS4.2.2 Implement and operate the ISMSThe organization shall do the following.d) Define how to measure the effectiveness of the selected controls or groups of controls and specify how these measurements are to be used to assess control effectiveness to produce comparable and reproducible results (see 4.2.3c)).
NOTE: Measuring the effectiveness of controls allows managers and staff to determine how well controls achieve planned control objectives.
4.2.3 Monitor and review the ISMS
The organization shall do the following.
a) Execute monitoring and reviewing procedures and other controls to:
1) promptly detect errors in the results of processing;
2) promptly identify attempted and successful security breaches and incidents;
3) enable management to determine whether the security activities delegated to people or implemented by information technology are performing as expected;
4) help detect security events and thereby prevent security incidents by the use of indicators; and
5) determine whether the actions taken to resolve a breach of security were effective.
b) Undertake regular reviews of the effectiveness of the ISMS (including meeting ISMS policy and objectives, and review of security controls) taking into account results of security audits, incidents, results from effectiveness measurements, suggestions and feedback from all interested parties.
c) Measure the effectiveness of controls to verify that security requirements have been met.
g) Update security plans to take into account the findings of monitoring and reviewing activities.
h) Record actions and events that could have an impact on the effectiveness or performance of the ISMS
(see 4.3.3). |
|
9 Performance evaluation
|
|
|
| 9.2 Internal auditThe organization shall conduct internal audits at planned intervals to provide information on whether the information security management system:a) conforms to1) the organization’s own requirements for its information security management system; and
2) the requirements of this International Standard;
b) is effectively implemented and maintained.
The organization shall:
c) plan, establish, implement and maintain an audit programme(s), including the frequency, methods, responsibilities, planning requirements and reporting. The audit programme(s) shall take into consideration the importance of the processes concerned and the results of previous audits;
d) define the audit criteria and scope for each audit;
e) select auditors and conduct audits to ensure objectivity and the impartiality of the audit process;
f) ensure that the results of the audits are reported to relevant management; and
g) retain documented information as evidence of the audit programme(s) and the audit results. |
|
6 Internal ISMS auditsThe organization shall conduct internal ISMS audits at planned intervals to determine whether the control objectives, controls, processes and procedures of its ISMS:a) conform to the requirements of this International Standard and relevant legislation or regulations;b) conform to the identified information security requirements;
c) are effectively implemented and maintained; and
d) perform as expected.
An audit programme shall be planned, taking into consideration the status and importance of the processes and areas to be audited, as well as the results of previous audits. The audit criteria, scope, frequency and methods shall be defined.
The selection of auditors and conduct of audits shall ensure objectivity and impartiality of the audit process.
Auditors shall not audit their own work.
The responsibilities and requirements for planning and conducting audits, and for reporting results and maintaining records (see 4.3.3) shall be defined in a documented procedure.
The management responsible for the area being audited shall ensure that actions are taken without undue delay to eliminate detected nonconformities and their causes. Follow-up activities shall include the verification of the actions taken and the reporting of verification results (see 8).
NOTE: ISO 19011:2002, Guidelines for quality and/or environmental management systems auditing, may provide helpful guidance for carrying out the internal ISMS audits.
4.2.3 Monitor and review the ISMS
The organization shall do the following.
e) Conduct internal ISMS audits at planned intervals (see 6).
NOTE: Internal audits, sometimes called first party audits, are conducted by, or on behalf of, the organization itself for internal purposes. |
|
9 Performance evaluation
|
|
|
| 9.3 Management reviewTop management shall review the organization’s information security management system at planned intervals to ensure its continuing suitability, adequacy and effectiveness.The management review shall include consideration of: a) the status of actions from previous management reviews;
b) changes in external and internal issues that are relevant to the information security management system;
c) feedback on the information security performance, including trends in:
1) nonconformities and corrective actions;
2) monitoring and measurement results;
3) audit results; and
4) fulfilment of information security objectives;
d) feedback from interested parties;
e) results of risk assessment and status of risk treatment plan; and
f) opportunities for continual improvement.
The outputs of the management review shall include decisions related to continual improvement opportunities and any needs for changes to the information security management system.
The organization shall retain documented information as evidence of the results of management reviews. |
|
7 Management review of the ISMS7.1 GeneralManagement shall review the organization’s ISMS at planned intervals (at least once a year) to ensure its continuing suitability, adequacy and effectiveness. This review shall include assessing opportunities for improvement and the need for changes to the ISMS, including the information security policy and information security objectives. The results of the reviews shall be clearly documented and records shall be maintained (see 4.3.3).7.2 Review input
The input to a management review shall include:
a) results of ISMS audits and reviews;
b) feedback from interested parties;
c) techniques, products or procedures, which could be used in the organization to improve the ISMS performance and effectiveness;
d) status of preventive and corrective actions;
e) vulnerabilities or threats not adequately addressed in the previous risk assessment;
f) results from effectiveness measurements;
g) follow-up actions from previous management reviews;
h) any changes that could affect the ISMS; and
i) recommendations for improvement.
7.3 Review output
The output from the management review shall include any decisions and actions related to the following.
a) Improvement of the effectiveness of the ISMS.
b) Update of the risk assessment and risk treatment plan.
c) Modification of procedures and controls that effect information security, as necessary, to respond to internal or external events that may impact on the ISMS, including changes to:
1) business requirements;
2) security requirements;
3) business processes effecting the existing business requirements;
4) regulatory or legal requirements;
5) contractual obligations; and
6) levels of risk and/or criteria for accepting risks.
d) Resource needs.
e) Improvement to how the effectiveness of controls is being measured.
4.2.3 Monitor and review the ISMS
The organization shall do the following.
f) Undertake a management review of the ISMS on a regular basis to ensure that the scope remains adequate and improvements in the ISMS process are identified (see 7.1). |
|
10 Improvement
|
|
|
| 10.1 Nonconformity and corrective actionWhen a nonconformity occurs, the organization shall:a) react to the nonconformity, and as applicable:1) take action to control and correct it; and
2) deal with the consequences;
b) evaluate the need for action to eliminate the causes of nonconformity, in order that it does not recur or occur elsewhere, by:
1) reviewing the nonconformity;
2) determining the causes of the nonconformity; and
3) determining if similar nonconformities exist, or could potentially occur;
c) implement any action needed;
d) review the effectiveness of any corrective action taken; and
e) make changes to the information security management system, if necessary.
Corrective actions shall be appropriate to the effects of the nonconformities encountered.
The organization shall retain documented information as evidence of:
f) the nature of the nonconformities and any subsequent actions taken, and
g) the results of any corrective action.
|
|
8 ISMS improvement8.2 Corrective actionThe organization shall take action to eliminate the cause of nonconformities with the ISMS requirements inorder to prevent recurrence. The documented procedure for corrective action shall define requirements for:
a) identifying nonconformities;
b) determining the causes of nonconformities;
c) evaluating the need for actions to ensure that nonconformities do not recur;
d) determining and implementing the corrective action needed;
e) recording results of action taken (see 4.3.3); and
f) reviewing of corrective action taken.
8.3 Preventive action
The organization shall determine action to eliminate the cause of potential nonconformities with the ISMS
requirements in order to prevent their occurrence. Preventive actions taken shall be appropriate to the impact
of the potential problems. The documented procedure for preventive action shall define requirements for:
a) identifying potential nonconformities and their causes;
b) evaluating the need for action to prevent occurrence of nonconformities;
c) determining and implementing preventive action needed;
d) recording results of action taken (see 4.3.3); and
e) reviewing of preventive action taken.
The organization shall identify changed risks and identify preventive action requirements focusing attention on
significantly changed risks.
The priority of preventive actions shall be determined based on the results of the risk assessment.
NOTE: Action to prevent nonconformities is often more cost-effective than corrective action. |
|
10 Improvement
|
|
|
| 10.2 Continual improvementThe organization shall continually improve the suitability, adequacy and effectiveness of the information security management system. |
|
8.1 Continual improvementThe organization shall continually improve the effectiveness of the ISMS through the use of the information security policy, information security objectives, audit results, analysis of monitored events, corrective and preventive actions and management review (see 7). |